Top 5 Cameras for Zoom Meetings
Tuesday, 03 May 2022
It’s more important than ever to have a high-quality camera. Keep reading to learn our top 5 cameras for Zoom meetings! As Zoom meetings are firmly here to stay for many professionals, having a high-quality camera is vital. After all, the last thing you want is a pixelated video and dodgy audio when you’re trying
- Published in Tech Blog
No Comments
Top 5 Ways Managed IT Services Can Help Your Business
Thursday, 07 April 2022
Over the years, we have helped hundreds of businesses by taking care of all their managed IT services so that they can focus on running their business. With a Cinch IT Support Plan, we handle everything for one easy to understand and predictable price. You no longer have to: Pay to train your IT employee(s):
- Published in Tech Blog
How to Find the Best Local Onsite Support
Wednesday, 16 March 2022
Offices use software and information technology for many purposes. Technical difficulties and other hiccups in the I.T. sector can disrupt your office workflow and result in financial losses. That’s why you need to know how to find the best local onsite support. Good local tech support can keep operations running smoothly and prevent technical issues.
- Published in Tech Blog
Top 5 Computer Monitors to Work from Home
Monday, 21 February 2022
Is your business set up to work from home? If so, you’ll need the right computer monitor to handle all your tasks. Granted, not all of us need the highest spec computer monitor, but you should still look for certain performance aspects at a baseline minimum. This article will review the top 5 computer monitors
- Published in Tech Blog
Cinch I.T. Named to MSP 500 List for 4th Consecutive Year
Monday, 14 February 2022
Cinch I.T. Recognized on CRN’s 2022 MSP 500 List Worcester, MA, February 14, 2022 — CRN®, a brand of The Channel Company, has named Cinch I.T. to its Managed Service Provider (MSP) 500 list in the Pioneer 250 category for 2022. CRN’s annual MSP 500 list identifies the leading service providers in North America whose
- Published in Company News
The Future of Cyber Attacks
Sunday, 13 February 2022
How have cyber attacks evolved over the past 12 months? Over the last 12-36 months, there has been a major split in the types of malicious attacks we’ve seen targeting businesses. While everyone anticipated an exponential increase in these attacks, the evolution into two predominant categories many support systems and security teams did not necessarily
- Published in Tech Blog
How CMMC 2.0 Impacts Managed Service Providers & Small Businesses
Monday, 24 January 2022
I.T. managed service providers (MSPs) are continuously looking for innovative ways of protecting small and medium-sized enterprises. The U.S. Department of Defense (DoD) has released a new version of their Cybersecurity Maturity Model Certification (CMMC) to protect against ransomware attacks, malware, and data leaks. CMMC 2.0 is a solid framework designed to defend businesses from
- Published in Tech Blog
Top 5 Antivirus Programs to Keep Your Computer Safe
Wednesday, 12 January 2022
Anyone who uses a computer needs to have antivirus programs. Even the safest computer users can accidentally let in threats, so having computer protection is a must. But finding the right program for your needs can be a minefield. You probably know the big names, but are they always the best? Not necessarily. If you’re
- Published in Tech Blog
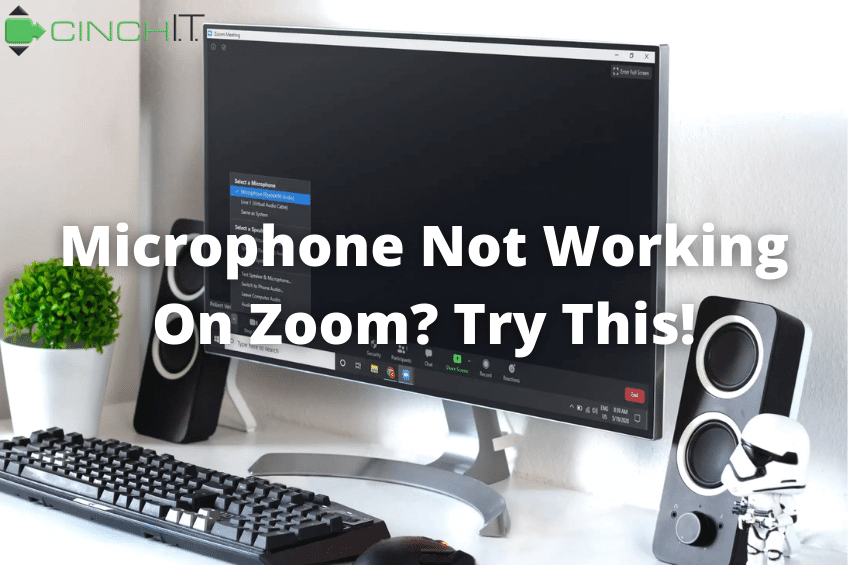
Microphone Not Working on Zoom? 13 Trouble Shooting Tips
Tuesday, 07 December 2021
Is your microphone not working on Zoom? Zoom audio problems can appear in several ways. This how-to guide troubleshoots common microphone not working on Zoom issues, including: Firstly, you can’t hear other people, or they can’t listen to you. Secondly, you can’t hear other people, but they can listen to you. Thirdly, you hear distorted
- Published in Tech Blog
Windows 11 Release: What to Know Before You Upgrade
Wednesday, 03 November 2021
The full Windows 11 release is finally here. With it comes many crucial updates to existing settings, programs, and desktop layout. So, what exactly does this new version have in store for users? Let’s take a look. Windows 11 Release: New Features There are many new features on the new Windows 11 release, including Microsoft
- Published in Tech Blog
Let's Connect
If you are a business owner who is plagued with slow computers, viruses, or email issues, then give Cinch IT a call.
Our consultative, proactive approach will help save you money and enhance productivity.

![Top 5 Cameras for Zoom Meetings [BANNER] - remote work support, teleconferencing, business I.T. support, Zoom cameras](https://cinchit.com/wp-content/uploads/2022/05/Top-5-Cameras-for-Professional-Zoom-Meetings-BANNER.png)